If you use LDAP authentication with your Netezza appliances, you’ll know how much effort goes into keeping your database permissions aligned to your corporate security policy. In this article we’ll show you how you can make life much easier by automating that process.
Lightweight Directory Access Protocol (LDAP) is a network protocol that provides a common language for servers and clients to communicate with each another. There are many LDAP implementations, the best known being Entra ID (formerly Active Directory), a directory service provided by Microsoft. Directory services are software programs that link databases in a network to manage the identities and security of users.
In any organisation where a Netezza system is connected to a network that uses LDAP authentication, there is quite a lot of manual intervention and coordination required by the LDAP administrator and the Netezza administrator.
User authentication is a 2-step process. Firstly, the Netezza system uses the user name and password that is stored on the LDAP server to authenticate a user. Following successful LDAP authentication, the Netezza system then confirms that the user account is defined on the Netezza system.
It’s the LDAP administrator who is responsible for adding and managing the user accounts and passwords and deactivating accounts on the LDAP server. But it is the Netezza administrator who is responsible for ensuring that each Netezza user is defined within the Netezza system catalog. The Netezza user names must match the user names that are defined in the LDAP server and if they don’t match, the Netezza administrator must manually change the user name to match the LDAP user name, or contact the LDAP administrator to change the LDAP user name. The Netezza Administrator must subsequently grant the user the correct permissions at the database level.
Let’s consider two organisations both running Netezza appliances that use LDAP authentication. One gets their Netezza administrators to manage user permissions manually, and the other deploys an LDAP synchronisation tool.
Managing LDAP Manually
Whenever the Netezza DBA receives a request to create a Netezza user account, they have to coordinate this with the LDAP administrator (as the user credentials must be identical). They must then define the user in the Netezza system catalog and grant the new user database level permissions according to their role. They will have to do this for every Netezza system that the user has access to.
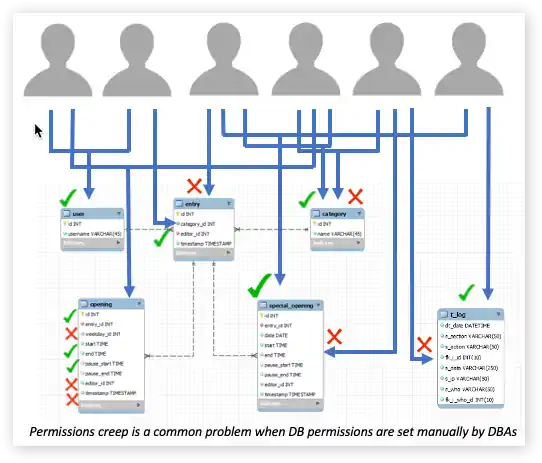
During the course of the user’s tenure the Netezza DBA may be asked to add or revoke permissions or remove the user. All the actions they perform to add, change or remove access are by physical commands. This is mostly done manually and is a tedious task that is prone to human error. This is especially true when access permissions have to be changed on scale, such as when an organisational restructure occurs.
The integrity of this process relies on three things. Firstly, the Netezza DBA is always kept in the loop when somebody joins or leaves the organisation or changes roles; secondly that they never deviate from the company’s security policy when granting access permissions; and thirdly that they don’t make mistakes or grant favours.
The consequences of omissions or errors can be quite far reaching. It is dangerous from a compliance perspective to have what are effectively phantom users enjoying continued access to a number of databases. In some cases, they may have quite elevated positions and be able to see quite sensitive data. They represent a vulnerability and some bad actor within an organisation can take control of the account and get access to information that they are not authorised to access. In any event, because the Netezza Administrator has the ability to grant access to objects manually, permissions creep can set in and users may end up with broader access than their role requires.
Managing LDAP with Smart Management Frameworks
Instead of manually setting up users, the Netezza DBA uses the Smart Access Control module of Smart Management Frameworks to synchronise Netezza’s user hierarchy to LDAP/Entra ID. Using a dynamic map that the DBA maintains, the organisation unit groups that are defined on the LDAP server are automatically created on the Netezza database(s), and all of the permissions associated with those groups in the map are automatically assigned to the groups. When a user leaves the organisation or is added to or removed from other groups, these changes dynamically trickle feed down to the database user level.
The Power of LDAP/AD Synchronisation
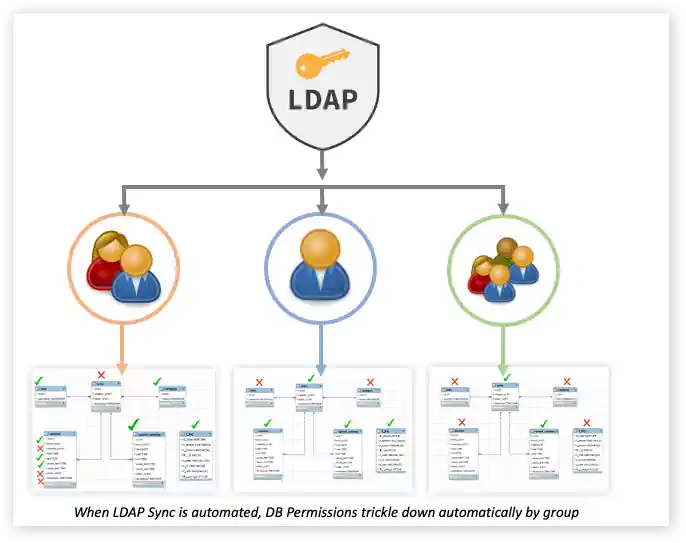
LDAP Synchronisation is really powerful because: 1 In addition to eliminating the repetitive and error-prone manual process, SMF provides a completely autonomous and separated audit regime that ensures that any permissions it finds that aren’t compliant with the corporate policy are reset to whatever the corporate policy is as determined by the LDAP server, and the naming conventions used in the LDAP server.
2 It reduces DBA administrative workload and improves productivity – you can imagine what a tedious task it is to have to constantly create and drop users, and reset passwords and grant remote permissions, all day long. And don’t forget you have to do this per appliance so if you are a large company that runs multiple Netezza systems, to have to do that at scale across all of them. 3 It allows for consistency between platforms – commonly, DBA’s will only tend maintain the permissions consistently in, say, a production environment and there will be a significant divergence across other similar environments like DR or Dev/Test. 4 It enables corporate customers to be compliant with governance legislation that enforces infosec type policy compliance (e.g. Sarbane Oxley).
If you are interested in learning more, check out the Smart Management Frameworks webpage, or feel free to contact us.